In a recent study, the average costs of data breaches continue to climb alarmingly. The research by the Ponemon institute reports that it has increased from 2.6% [USD 4.24 million in 2021] to USD 4.35 million in 2022.
On the one hand, it is easy to confuse that data protection is essential only for giant corporations. On the other hand, unsurprisingly, most leading organizations invest considerable efforts in crafting data security policies with well-appointed mandates, a manageable scope, and cross-functional teams.
But even smaller businesses are not immune in today’s climate. And that responsibility falls on the IT departments.
IT’s Role in Data Security Policy
IT departments are seen as custodians when providing the means and methods for creating, storing, sending, and retrieving business-related information. By definition, “protect” includes
- preventing unauthorized access,
- the uncontrolled alteration, and
- unlawful destruction.
While most IT teams understand that data integrity is critical for a business, the challenge comes from the need to strike a ‘wise’ balance between vital data security interests and overhead costs.
Data Privacy and Data Security.
While the two terms are used interchangeably (and share a complementary relationship), they are two separate concepts.
Data security includes the physical protection of Personally Identifiable Information (PII)and how companies protect it from cyberattacks and other data breaches.
On the other hand, data privacy covers policies and procedures safeguarding the collection, storage, and dissemination of PII and a company’s proprietary (often confidential) information.
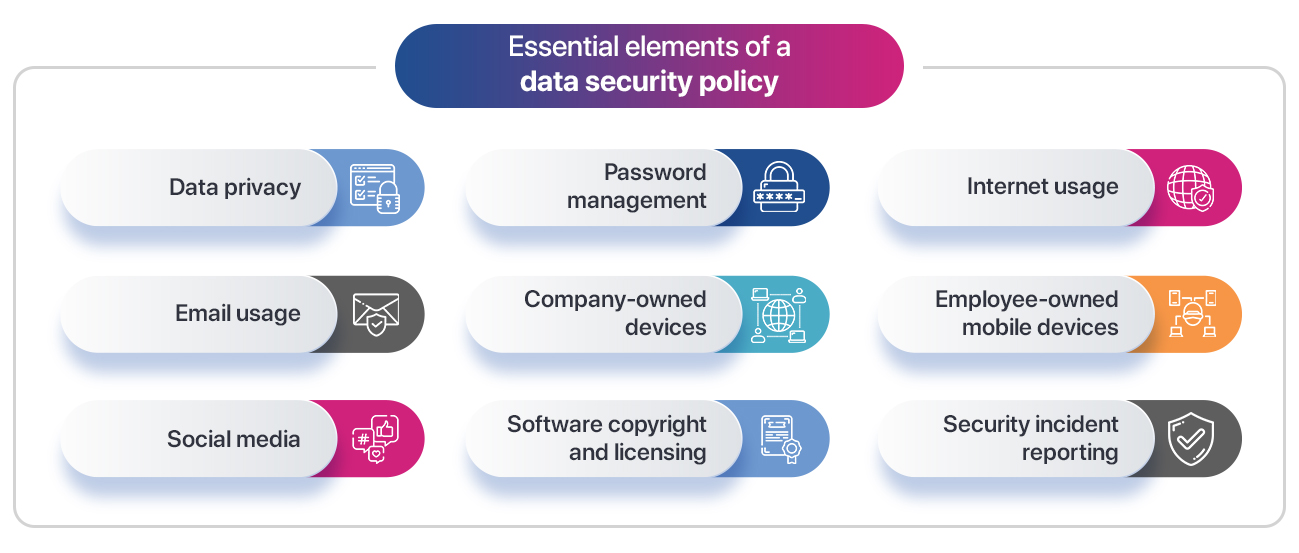
Elements of Data Security Policy
Data security policy is essential for companies from two perspectives: Human resources and Information Technology.
Both policymakers and reviewers can gain from contextualizing the below elements to their organization’s needs.
People-Related.
In this theme, the Data security policy covers everything from usage norms governing company resources for personnel to adhering to various IT compliance, including establishing appropriate passwords (length and complexity).
Also crucial to the policy is E-Mail administration, and the encryption standards that protect employees, vendors, and customers’ e-mails from phishing and other cyber-attacks are also essential to the procedure.
Another key people element aspect of the Data Security Policy involves Internet-based Social Networking and the extent of using it.
Finally, the policy must call out how employees and other parties are to report breaches and the corresponding investigation protocols.
Technology-Related
Most data security rules stipulate the need for the physical and logical protection of IT assets such as servers, routers, firewalls, and more.
After all, rebuilding or replacing a server that has crashed or been compromised is much easier if you can reliably back up, restore, and manage server configurations.
Additionally, access of mobile devices (employees, contractors, visitors, or others) to the parent network is a critical component of an organization’s Data security policy. Next on the list are the encryption mandates – selective or comprehensive.
Lastly comes the management and supervision of access controls for hardware and software, including multi-factor authentication and remote access. This section of the Data Security policy includes keeping track of all software purchases, installations, usage, licensing terms, and expenses.
Data security graphics – information privacy and safe storage technology concept. Word cloud.
Risk implications with an ineffective Data Security Policy.
- A breach in security can hurt a company’s reputation, discouraging potential consumers. In today’s age, the severity of data breaches can be experienced in the immediate social media backlashes.
- The costly downtime increases the opportunity cost when security breaches strike. A company’s productivity and revenue are negatively impacted. By 2021, the average data breach cost had risen to $4.24 million, a 10% increase from the previous year’s figure. Another survey indicated that when a company uses remote workers (because of a breach), the average cost increases to $4.96 million.
- Adding to reputational and financial risk are the legal implications. Be it through penalties, legal action, or even end-customer compensation, suffering companies can sue the ‘data-breached’ company for heavy damages. In some aggravated cases, the losses may extend to patents, blueprints, and other certifications, not to mention customer PII. Adding to the price tag mentioned are also investments in buying extra insurance that covers legal costs.
- Along with data loss, the fourth significant risk that a weak data security policy can invite is identity theft and fraud. These losses may include sensitive data such as IP addresses, contact details, and financial details.

Data security graphics – information privacy and safe storage technology concept. Word cloud.
Conclusion
A company’s data is an essential commodity that must be safeguarded at all costs. The complexity and rapid change of data privacy standards that every company must follow further add to the difficulty.
In that regard, apart from firming up official data protection policies, associated safeguards like – staff training, education, data backups, and investments in new-age software security measures are indispensable in the longer term.